Cybersecurity Insights & Best Practices
We want to share with our clients and partners various insights and recommendations we’ve learned while aiming to enhance our own cybersecurity best practices. Much of this information is courtesy of a custodial partner who recently hosted an eye-opening cybersecurity webcast. We have prepared these recommendations solely for informational purposes based on information received from that custodian, as well as guidance and best practices from our own IT Department. Other recommendations are gleaned from cybersecurity awareness training our firm has received after engaging outside vendors for additional education and testing.
Back in September, we shared guidance on steps to take to mitigate the potential risk arising from the Equifax breach. We suggested clients enroll in credit monitoring, consider credit freezes, and closely monitor financial accounts for unfamiliar transactions. With the information already out, these steps were intended to combat the use of compromised information. Credit monitoring, while helpful, is insufficient, as a cybercriminal who is monitoring your communications can conceivably intercept alerts from your credit monitoring service and even impersonate you in the effort to remove obstacles to theft. Again, we come back to the need to secure access to your communications and cripple a criminal’s ability to “act” as you.
Finally, once in possession of your information, sophisticated and patient cybercriminals may lay in wait for years until moving on your information and assets. While we urge all clients to review and adopt the best practices discussed in this letter, the most practical defense – and our best single piece of advice - is to pursue a credit freeze. This article from the Consumer Financial Protection Bureau outlines the steps in that process.
TODAY’S CYBER-SECURITY LANDSCAPE
The news this fall of the Equifax breach raised significant public awareness of cybersecurity risks due to the sensitivity of the data and the sheer volume of information exposed in the breach. An estimated 143 million Americans were affected, and the dark web was flooded with compromised information; as we heard on the webcast, it now costs as little as $20 to purchase personal information on the internet’s “black market.” The actual impacts – that is, the financial losses and other consequences from criminal use of this data – are unknowable at this point and may be for some time.
Equifax may have been the most high-profile example, but identify theft is certainly not a new threat – it is simply made easier by the internet, where we constantly input and often store the exact information needed to perpetrate theft. The below statistics are stunning, and yet they were gathered “pre-Equifax:”

At WST, our cybersecurity efforts are robust, constantly evolving and a critical focus for our firm. On our side, we are taking steps aimed at safeguarding the information that is in our possession, both by beefing up our own network security and also training our staff to be practitioners of cybersecurity best practices. High-touch client service has always been our goal, but today’s cybersecurity landscape dictates that we take all measures necessary to properly verify that we are taking direction from our clients and authorized parties – not cybercriminals.
However, as our industry is learning, motivated cybercriminals adapt and proliferate new strategies at a pace that is challenging for any organization to meet. While verification and a deep knowledge of our clients can help detect fraud once it has occurred, the theft of your identity lays the groundwork for financial crimes and generally occurs prior to contact with your financial institution. Ultimately client education is the best defense against financial loss arising from identity theft.

As the below infographic lays out, cybercriminals take a variety of approaches to acquiring your data. These approaches vary in sophistication, and some rely on the success of others. Phishing is highlighted, as it is believed to be the most prevalent and it is also the foundation for more sophisticated approaches.
Phishing is also considered the least sophisticated approach, relying on our lack of attention to detail or – increasingly – our inability to spot suspicious information. Social engineering and call forwarding are highly involved approaches that rely on prolonged personal interaction (both with the victim and in the process of impersonating the victim).
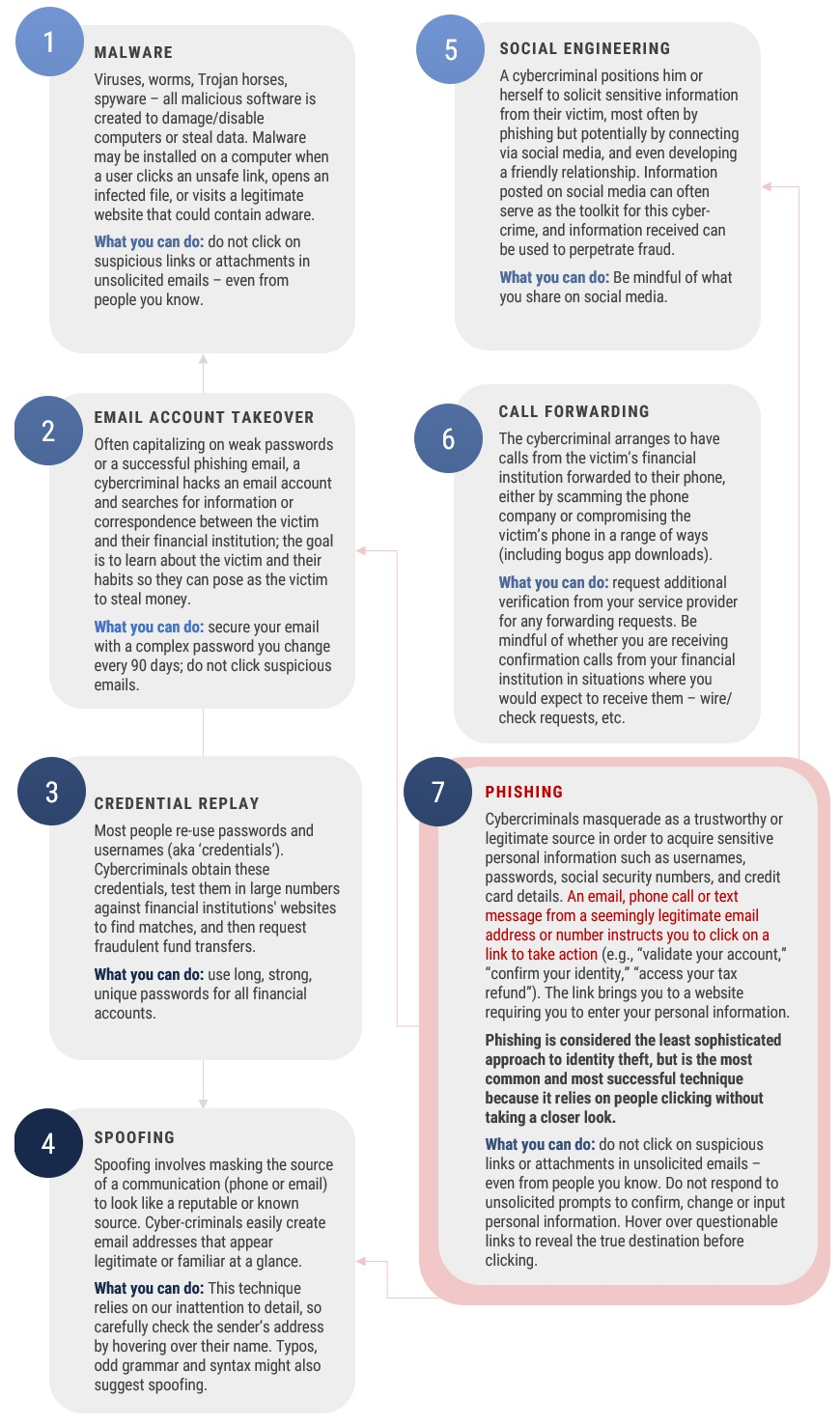
In the webcast, the custodian shared reports of cybercriminals:
- Luring security-conscious victims into phishing attacks by sending fake cybersecurity alerts
- Rerouting victims’ calls to fraud centers back to themselves
- Convincing or bullying customer service associates into cutting corners on verification protocols by complaining angrily about the inconvenience these safeguards represent
- Hacking company websites and substituting corporate contact information for email addresses, phone numbers and other channels controlled by the hacker
What can be done? Our best practices:
- Make sure the email sender is legitimate
- Closely inspect the name of the sender by hovering over or (on mobile) clicking into the Sender Name, noting that an email might be off by just a single letter in either the name or the “@organization” part
- If you’re unsure but the email looks familiar, do a quick search of your email history to check that the information lines up
- Never click on strange links or attachments in unsolicited emails – even from friends. Malware is often transmitted through infected files – especially PDFs
- Where possible, avoid following links at all; navigating to a site through your browser should mitigate risk in most cases
- Never click or use contact information supplied in suspicious-looking emails from service providers
- Look for odd grammar, misspellings, and deviations from the familiar format and content of marketing, customer service, news, or other emails you receive regularly
- Never open or click security notifications or unsolicited password re-set emails

Passwords
- Long, strong, unique and changed frequently – especially for your email, which is where you typically receive password re-set communications from other sites. Suggestions:
- Opt to use “the strong password generator” feature that is embedded in many devices
- Install a Password Manager to keep track of auto-generated/ encrypted passwords
- Password Managers require one “master” password to unlock access to all others
- Apple’s Touch ID mechanism for accessing stored passwords is one example
- Password Managers are not ironclad but generally are safe, especially if the hacker does not have access to the physical device
- Never reuse passwords across sites; if you decline to use generated passwords, consider establishing a complicated but memorable “logic” that you apply based on the name of the organization. Furthermore, you might consider varying this logic based on the type of site you are accessing.
Dealing with service providers – banks, utilities, cable company, etc.
- Familiarize yourself with the way your service provider reaches you if they need to verify details or gather personal information. People each year receive calls from criminals purporting to be the IRS – the IRS does NOT place calls under any circumstances
- Inform the service provider immediately if you receive a suspicious call or email from someone claiming to represent that company
- Ask your service providers about the most secure ways to access information – website vs. application, etc.
- Add provider contact information into your address book, which should prevent you from inadvertently using fraudulent contact information supplied in phishing emails or swapped into hacked websites.
Financial accounts
- Familiarize yourself with the methods by which your bank or advisor accepts instructions or authorization of trades, transfers or wires
- Ask what methods are authorized on your account for all types of instructions; consider restricting these instructions, balancing the convenience of email against the security of phone calls
- Talk to your Client Service contacts about using subliminal verifications in addition to regular protocols, especially in dealing with wires, transfers or movements of assets; examples would be details of your last meeting or anything that you would not have discussed over email or shared over social media.
Surf Safely!
- Public Wi-Fi
- These networks are goldmines for hackers; be cautious in your usage
- Become familiar with settings on your mobile devices, which may automatically connect you to unknown public Wi-Fi
- Browsing
- Hover over questionable links to reveal the true destination before clicking
- Even if on your personal device, be sure to log out completely (which terminates access) when exiting all websites to prevent cybercriminals from obtaining your personal information
- Social media - limit what you share and with whom:
- Consider sanitizing social media profiles of information that could support identify theft efforts – home address, cell phone number, workplace, vacation plans, etc.
- At a minimum, consider restricting the viewability of this information to people whom you’re either connected to or closely removed from within a given network
- Be selective in accepting requests to connect
- Be cautious in engaging with anyone who isn’t a “real-life” acquaintance - especially unsolicited contacts with few or no connections in your network
- Downloading applications
- Ensure you are downloading legitimate apps from trusted publishers
- Most application hubs show the number of ratings for each application; unrated applications or applications with few ratings should be closely scrutinized, especially if the application is widely used
Conclusion
We are providing this information in the effort to prepare – not to alarm – our clients and partners. Cybersecurity threats are real, constant and complex, but they can be combatted effectively through a high level of personal vigilance and increased communication with the organizations entrusted with your information and assets. As always, we invite you to reach out to us with feedback, suggestions, questions or simply more information on how to mount your best defense.
Sources: WST, summarizing information provided by Charles Schwab & Co., including in a Cybersecurity Webcast January 19, 2018, and KnowBe4, a cybersecurity education vendor.
Besides attributed information, this material is proprietary and may not be reproduced, transferred or distributed in any form without prior written permission from WST. WST reserves the right at any time and without notice to change, amend, or cease publication of the information. This material has been prepared solely for informative purposes. The information contained herein may include information that has been obtained from third party sources and has not been independently verified. It is made available on an “as is” basis without warranty. This document is intended for clients for informational purposes only and should not be otherwise disseminated to other third parties. Past performance or results should not be taken as an indication or guarantee of future performance or results, and no representation or warranty, express or implied is made regarding future performance or results. This document does not constitute an offer to sell, or a solicitation of an offer to purchase, any security, future or other financial instrument or product.
